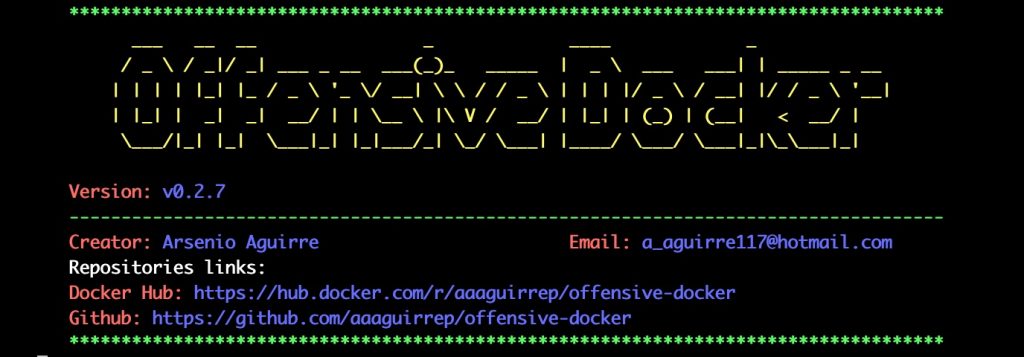
Offensive Docker is an image with the more used tools to create an pentest environment easily and quickly.
![]() Note: Check out the next repo to know how to launch offensive docker in a VPS in Google Cloud Platform or Digital Ocean (free credit included). Offensive Docker VPS
Note: Check out the next repo to know how to launch offensive docker in a VPS in Google Cloud Platform or Digital Ocean (free credit included). Offensive Docker VPS
Table of Contents
- Links
- Features
- Requirements
- Tools installed
- Documentation
- Usage
- Nice configurations
- Environment tested
- Warning
- Donations
- Contributors
- Contributing
- Stargazers over time
- License
Links
 Video: Demos
Video: Demos Chat: Discord
Chat: Discord VPS Automation
VPS Automation Advanced configurations
Advanced configurations
Features
- OS, networking, developing and pentesting tools installed.
- Connection to HTB (Hack the Box) vpn to access HTB machines.
- Popular wordlists installed: SecLists, dirb, dirbuster, fuzzdb, wfuzz and rockyou.
- Proxy service to send traffic from any browsers and burp suite installed in your local directory.
- Exploit database installed.
- Tool for cracking password.
- Linux enumeration tools installed.
- Tools installed to discovery services running.
- Tools installed to directory fuzzing.
- Monitor for linux processes without root permissions
- Zsh shell installed.
Requirements
- Docker service installed
Tools installed
Operative system tools
- rdate
- vim
- zsh
- oh-my-zsh
- locate
- cifs-utils
- htop
- tree
- gotop
Network tools
- traceroute
- telnet
- net-tools
- iputils-ping
- tcpdump
- openvpn
- whois
- host
- prips
- dig
Developer tools
- git
- curl
- wget
- ruby
- go
- python
- python-pip
- python3
- python3-pip
- php
- aws-cli
- tojson
- nodejs
 Offensive tools
Offensive tools
Port scanning
 Recon
Recon
Subdomains
Subdomain takeover
DNS Lookups
 Screenshot
Screenshot
 Crawler
Crawler
 Search directories
Search directories
Fuzzer
Web Scanning
CMS
Search JS
Wordlist
Git repositories
OWASP
 Mobile
Mobile
Brute force
Cracking
OS Enumeration
- htbenum
- linux-smart-enumeration
- linenum
- enum4linux
- ldapdomaindump
- PEASS – Privilege Escalation Awesome Scripts SUITE
- Windows Exploit Suggester – Next Generation
- smbmap
- pspy – unprivileged Linux process snooping
- smbclient
- ftp
Exploits
Windows
Reverse shell
Other resources
- pentest-tools from @gwen001
- qsreplace from @tomnomnom
Custom functions
- NmapExtractPorts from @s4vitar
Other services
- apache2
- squid
 Documentation
Documentation
See the project’s wiki for documentation.
 Usage
Usage
You can use the docker image by the next two options:
Option 1 – Use the github repository
git clone --depth 1 https://github.com/aaaguirrep/offensive-docker.git
cd offensive-docker
docker build -t offensive-docker .
docker run --rm -it --name my-offensive-docker offensive-docker /bin/zsh
Option 2 – Use the image from docker hub
Use image from docker hub: aaaguirrep/offensive-docker
docker pull aaaguirrep/offensive-docker
docker run --rm -it --name my-offensive-docker offensive-docker /bin/zsh
Considerations to run the container
There are differents use cases for use the image and you should know how to run the container properly.
- Use the container to access HTB (Hack the Box) machines by HTB vpn.
docker run --rm -it --cap-add=NET_ADMIN --device=/dev/net/tun --sysctl net.ipv6.conf.all.disable_ipv6=0 --name my-offensive-docker aaaguirrep/offensive-docker /bin/zsh - Share information from your local directory to container directory and save information on your local directory. You should save information under /offensive directory.
docker run --rm -it -v /path/to/local/directory:/offensive --name my-offensive-docker aaaguirrep/offensive-docker /bin/zsh - Expose internal container services (apache, squid) for your local environment.
docker run --rm -it --name my-offensive-docker -p 80:80 -p 3128:3128 aaaguirrep/offensive-docker /bin/zshInside the container start apache2 and squid services by the aliases.apacheUp squidUp - Mount directories by umount command.
docker run --rm -it --privileged --name my-offensive-docker aaaguirrep/offensive-docker /bin/zsh - Tools are downloaded in /tools directory.
 Nice configurations
Nice configurations
You can set up the docker image with nice configurations like as:
1. Configure credentials in the docker
To use access keys, tokens or API Keys in the docker review the next repo Offensive Docker Custom
2. Alias to connect to HTB (Hack the Box) VPN
To use both options you should use -v option to map local directoty with /offensive container directory.
Option 1 – HTB VPN using github repository
Add the next line in step “Create shorcuts” in Dockerfile, build a new image and run a new container with the -v option.
RUN echo "alias vpnhtb=\"openvpn /offensive/path/to/ovpn/file\"" >> /root/.zshrc
Option 2 – HTB VPN using docker hub image
Create a new Dockerfile with the next steps, build a new image and run a new container with -v option.
FROM aaaguirrep/offensive-docker
# Create a shortcut and load the ovpn file from workstation
RUN echo "alias vpnhtb=\"openvpn /offensive/path/to/ovpn/file\"" >> /root/.zshrc
3. Save and load command history in your local environment
When you delete a container all information is deleted incluide command history. The next configuration provides you an option for save the command history in your local environment and load it when you run a new container. So, you wont lose your command history when run a new container.
To use both options you should use -v option to map local directoty with /offensive container directory.
Option 1 – Command history using github repository
Add the next line in step “Create shorcuts” in Dockerfile, build a new image and run a new container.
# Save and load command history in your local environment
RUN sed -i '1i export HISTFILE="/history/.zsh_history"' /root/.zshrc
Option 2 – Command history using docker hub image
Create a new Dockerfile with the next steps, build a new image and run a new container.
FROM aaaguirrep/offensive-docker
# Save and load command history in your local environment
RUN sed -i '1i export HISTFILE="/history/.zsh_history"' /root/.zshrc
 Environment tested
Environment tested
The image was tested in the following environments:
- Docker service for Mac: Docker version 19.03.5, build 633a0ea
- Docker service for Linux instance on Google Cloud Platform: Docker version 19.03.6, build 369ce74a3c
- Docker service for Linux droplet on Digital Ocean: Docker version 19.03.6, build 369ce74a3c
 Warning
Warning
- Do not save information on container directories because it will be lost after delete the container, you should save information in your local environment using the parameter -v when you run the container. For instance:
docker run --rm -it -v /path/to/local/directory:/offensive --name my-offensive-docker aaaguirrep/offensive-docker /bin/zshThe above command specify a path local directory mapped with /offensive container directory. You should save all information under /offensive directory. - Use hashcat and john the ripper on controlled environments as CTF. You can experiment issues.